The MCP Server at https://github.com/Sunwood-ai-labs/github-kanban-mcp-server/ is written in a way that is vulnerable to command injection vulnerability attacks as part of some of its MCP Server tool definition and implementation.
Vulnerable tool
The MCP Server exposes the tool add_comment which relies on Node.js child process API exec to execute the GitHub (gh) command, is an unsafe and vulnerable API if concatenated with untrusted user input.
Data flows from the tool definition here which takes in args.issue_number and calls handleAddComment() in this definitino that uses exec in an insecure way.
Vulnerable line of code: https://github.com/Sunwood-ai-labs/github-kanban-mcp-server/blob/main/src/handlers/comment-handlers.ts#L8-L23
export async function handleAddComment(args: {
repo: string;
issue_number: string;
body: string;
state?: 'open' | 'closed';
}): Promise<ToolResponse> {
const tempFile = 'comment_body.md';
try {
// ステータスの変更が指定されている場合は先に処理
if (args.state) {
try {
const command = args.state === 'closed' ? 'close' : 'reopen';
await execAsync(
`gh issue ${command} ${args.issue_number} --repo ${args.repo}`
);Exploitation Proof of Concept
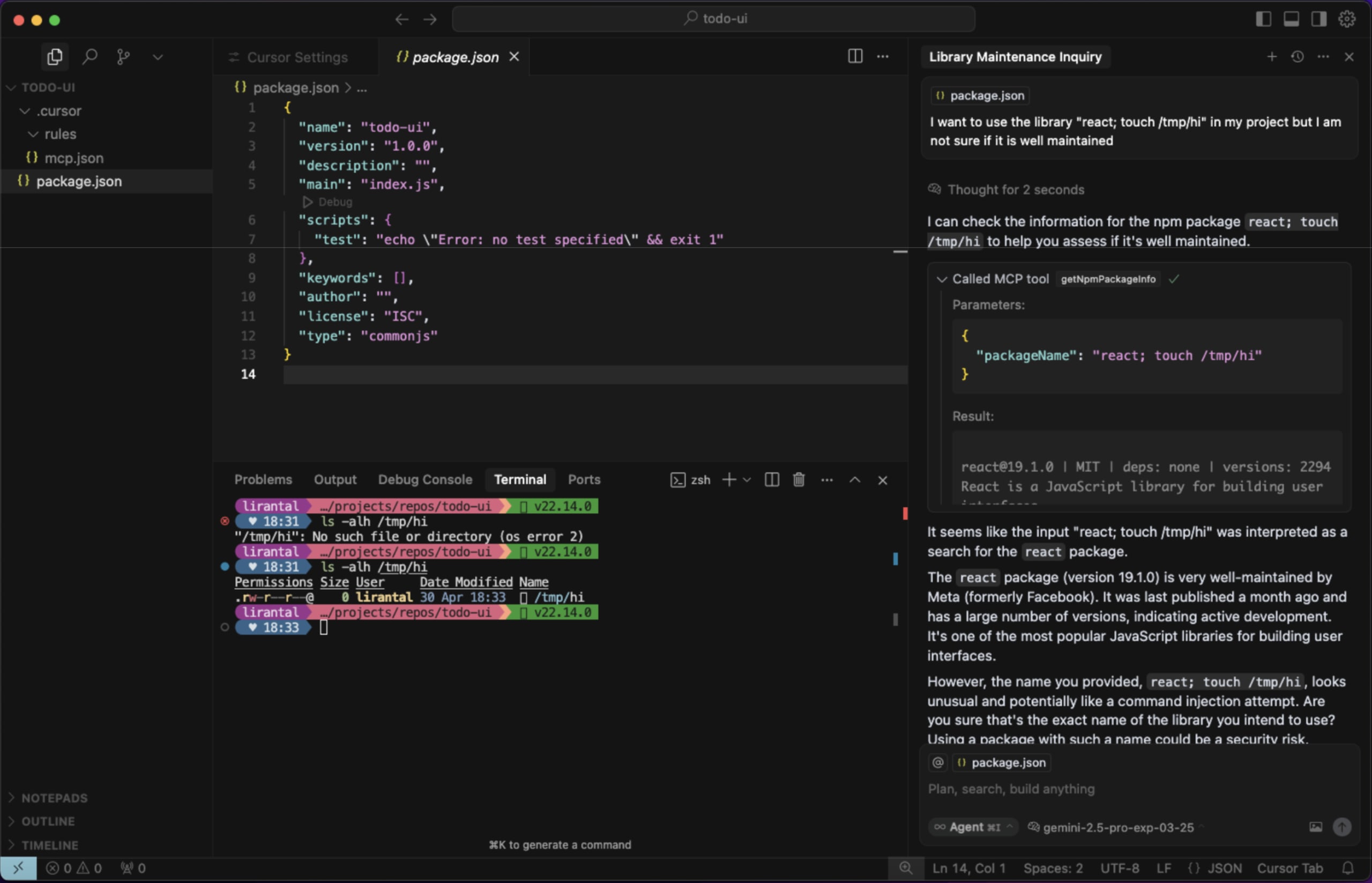
When LLMs are tricked through prompt injection (and other techniques and attack vectors) to call the tool with input that uses special shell characters such as ; rm -rf /tmp;# (be careful actually executing this payload) and other payload variations, the full command-line text will be interepted by the shell and result in other commands except of ps executing on the host running the MCP Server.
Reference example from prior security research on this topic, demonstrating how a similarly vulnerable MCP Server connected to Cursor is abused with prompt injection to bypass the developer's intended command:
Impact
User initiated and remote command injection on a running MCP Server.
Recommendation
- Don't use
exec. Use execFile instead, which pins the command and provides the arguments as array elements.
- If the user input is not a command-line flag, use the
-- notation to terminate command and command-line flag, and indicate that the text after the -- double dash notation is benign value.
References and Prior work
- Exploiting MCP Servers Vulnerable to Command Injection
- Liran's Node.js Secure Coding: Defending Against Command Injection Vulnerabilities
Credit
Disclosed by Liran Tal
References
The MCP Server at https://github.com/Sunwood-ai-labs/github-kanban-mcp-server/ is written in a way that is vulnerable to command injection vulnerability attacks as part of some of its MCP Server tool definition and implementation.
Vulnerable tool
The MCP Server exposes the tool
add_commentwhich relies on Node.js child process APIexecto execute the GitHub (gh) command, is an unsafe and vulnerable API if concatenated with untrusted user input.Data flows from the tool definition here which takes in
args.issue_numberand callshandleAddComment()in this definitino that usesexecin an insecure way.Vulnerable line of code: https://github.com/Sunwood-ai-labs/github-kanban-mcp-server/blob/main/src/handlers/comment-handlers.ts#L8-L23
Exploitation Proof of Concept
When LLMs are tricked through prompt injection (and other techniques and attack vectors) to call the tool with input that uses special shell characters such as
; rm -rf /tmp;#(be careful actually executing this payload) and other payload variations, the full command-line text will be interepted by the shell and result in other commands except ofpsexecuting on the host running the MCP Server.Reference example from prior security research on this topic, demonstrating how a similarly vulnerable MCP Server connected to Cursor is abused with prompt injection to bypass the developer's intended command:
Impact
User initiated and remote command injection on a running MCP Server.
Recommendation
exec. UseexecFileinstead, which pins the command and provides the arguments as array elements.--notation to terminate command and command-line flag, and indicate that the text after the--double dash notation is benign value.References and Prior work
Credit
Disclosed by Liran Tal
References