Personal digital firewall ruleset for Surge, focused on identifying potential communication threats at both the application layer and transport layer. It covers a broad range of suspicious behaviors including DNS poisoning, Malware IOC, SDK telemetry, backdoor communication, PCDN relay communication, C2 controllers, and other potentially malicious communications.
The project also expands domain-based identification to major global advertising platforms, behavioral tracking services, and adult content sites. It helps users achieve precise local traffic identification and classification on iOS and macOS, and define routing strategies based on their own needs.
In addition, the project incorporates rule sets targeting globally recognized high-risk threat infrastructures, including detection strategies for Pegasus spyware and its associated command-and-control infrastructure.
The project fully enforces encrypted DNS, rejecting plaintext queries to ensure secure and private communications. Even on devices lacking traditional security software — such as iPhones — Aegis provides effective protection at the network traffic layer.
The Aegis rule set is dedicated to identifying and classifying the following high-risk communication behaviors:
- Ad domain identification, behavioral tracking, and surveillance-style CDN nodes
- PCDN relay traffic and shared-bandwidth transmission
- Botnets, remote access Trojans, and malware C2 channels
- SDK telemetry and behavioral fingerprinting
- APT command-and-control (C2) infrastructure
- DNS poisoning / injection / hijacking behavior
Aegis is purpose-built for the Surge platform, fully compatible with both iOS and macOS. It offers high readability, auditability, and modular deployment — making it suitable for policy-based routing, communication analysis, and enhanced security configurations.
An optional advanced module CA_Block.list is also available, designed to block globally controversial or publicly revoked root certificate authorities, OCSP responders, and CRL domains. This module is intended for users with heightened digital trust requirements and provides additional protection against man-in-the-middle attacks and malicious certificate chains.
Aegis adheres to technical neutrality, information transparency, and independent autonomy. I firmly believe every individual has the right to understand and control their network traffic. Therefore, Aegis does not accept any form of commercial investment or capital control. To ensure purity, trust, and security, all configurations are handcrafted and audited by me, with complete annotations to guarantee every rule is transparent, verifiable, and pollution-free.
| Module ID | Module Name | File Name | Description | Criteria |
|---|---|---|---|---|
| ① | Untrusted Certificate Authorities | CA_Block.list | Flags CA root certificates, OCSP endpoints, and CRL domains with known incidents of misuse or revocation. Recommended for scenarios requiring enhanced digital trust. (Advanced Module – Disabled by Default) | Involves cases of certificate misuse, unauthorized issuance, or public revocation records |
| ② | Advertising Domain Detection | AdDomain.list | Covers domains used in commercial advertising delivery, social pixel tracking, behavioral analytics, and third-party SDK statistics (Identification Module - Disabled by Default) | Identified based on behavioral patterns and data collection models, distinguished from telemetry-related communications |
| ③ | Adult Content Domain Detection | AdultDomain.list | Covers domains related to major global adult content platforms (Identification Module - Disabled by default) | Domains directly associated with adult content distribution |
| ④ | PCDN Communication Detection | PCDNDomain.list | Identifies link behaviors suspected to use “shared bandwidth” models, involving device relays, cache nodes, and distributed delivery networks (Identification Module - Disabled by Default) | Identified based on traffic patterns and node distribution consistent with multi-hop relay and cache characteristics |
| ⑤ | Traffic Inspection & Node Detection | InspectionDomain.list | Detects active network-level interventions such as DPI probing, DNS poisoning, HTTP injection, and MITM eavesdropping (Identification Module - Disabled by Default) | Identified based on traffic anomalies like tampering, redirection, and injection, commonly seen in manipulated network environments |
| ⑥ | Behavioral Analytics / Telemetry Node Detection | BehaviorDomain.list | Flags cloud service nodes with identifiable behavioral fingerprinting, including telemetry SDKs, analytics platforms, and behavioral modeling services (Identification Module - Disabled by Default) | Focused on behavior-analytic SDK communication patterns via DNS/TLS traffic; excludes ad or data-upload SDKs |
| ⑦ | Background Reconnections & Silent Communication Blocking | Background_Block.list | Identifies domains used by IoT, NAS, or SDKs for config uploads or device callbacks, aiding detection of stealth telemetry communications (Blocking Module – Enabled by Default) | Focused on background connection behavior via callback frequency, paths, and data uploads; excludes ad and analytics SDKs |
| ⑧ | Backdoor Control & Implant Communication Blocking | Backdoor_Block.list | Blocks known malicious infrastructure involving remote access tools (RATs), reverse shells, heartbeat signals, etc. (Blocking Module – Enabled by Default) | Clearly associated with malicious traffic or exploit backdoors |
| ⑨ | Botnet & Command Node Blocking | Botnet_Block.list | Blocks known botnet controllers, DDoS nodes, and mass-control infrastructure (Blocking Module – Enabled by Default) | Based on public threat intelligence with confirmed attribution and verifiable IoCs |
| ⑩ | Malware IOC Blocking | Malware_IOC_Block.list | Blocks communication domains, IPs, and control infrastructure associated with known malware families, toolchains, and related attack activities (Blocking Module – Enabled by Default) | Derived from public threat intelligence, malware sample analysis, and verifiable research data |
| ⑪ | Pegasus Spyware Communication Blocking | Pegasus_Block.list | Contains domains disclosed by Amnesty used by Pegasus spyware for C2 communication (Blocking Module – Enabled by Default) | Based on Amnesty’s public disclosures of Pegasus C2 infrastructure, indicating high surveillance risk |
| ⑫ | Phishing Domain Blocking | Phishing_Block.list | Blocks domains associated with phishing attacks, including spoofed login pages, fake official sites, and links in deceptive emails. Typical targets of social engineering campaigns. (Blocking Module – Enabled by Default) | Based on public threat intelligence with confirmed attribution and verifiable IoCs |
| ⑬ | Scam Domain Blocking | Scam_Block.list | Blocks suspicious domains with extremely low reputation, reported fraud, fake services, or user complaints. (Blocking Module – Enabled by Default) | Based on public threat intelligence with confirmed attribution and verifiable IoCs |
| ⑭ | Risk Communication Observation List | Quarantine_Block.list | Covers domains and IPs that are not yet confirmed as malicious but exhibit anomalous communication behaviors, including opaque purposes or the use of non-public protocols or non-standard ports. A quarantine-based blocking strategy is applied by default to mitigate potential risks.(Observation Module – Enabled by Default) | Identified through anomalous communication behavior analysis; the risk has not been conclusively classified as malicious and is placed under isolation and observation for further review |
Aegis is hosted on GitHub with an automated update mechanism, ensuring that all rule sets remain up-to-date and are fully compatible with remote subscription in Surge.
If configuration auto-reload is not enabled, you can manually refresh external resources or reload the profile to ensure the ruleset stays up to date.
Aegis follows Semantic Versioning: vMAJOR.MINOR.PATCH.
Example: Aegis v3.0.1, where MAJOR=3, MINOR=0, and PATCH=1.
MAJOR (X): Major structural or compatibility changes 👉 You must re-download the configuration and re-add the nodes.
MINOR (Y): New policy groups, new modules, or new features 👉 It is recommended to re-download the configuration and re-add the nodes.
PATCH (Z): Rule fixes, annotation updates, or minor optimizations 👉 No need to re-download the configuration; updating external resources is sufficient.
Important
It is recommended to enable 「Automatically reload if the profile was modified externally/remotely」. This option only applies to automatic reloading when the configuration file (.conf) changes. PATCH updates still require manually refreshing external resources (RULE-SET) to take effect.
Note
Current version: Aegis v2.0.0. Previous version: Aegis v1.3.4. This is a MAJOR update (MAJOR = 2). You must re-download the configuration and re-add the nodes. External resources will be updated automatically.
Current version: Aegis v2.3.0. Previous version: Aegis v2.2.4. This is a MINOR update (MINOR = 3). It is recommended to re-download the configuration and re-add the nodes. External resources will be updated automatically.
Current version: Aegis v3.3.4. Previous version: Aegis v3.3.3. This is a PATCH update (PATCH = 4). No need to re-download the configuration. You only need to refresh external resources.
Tip
As long as you re-download the configuration file (.conf) and re-add the nodes, external resources will be updated automatically if the option 「Automatically reload if the profile was modified externally/remotely」 is enabled.
For PATCH version updates, you still need to manually refresh external resources (RULE-SET) for the changes to take effect.
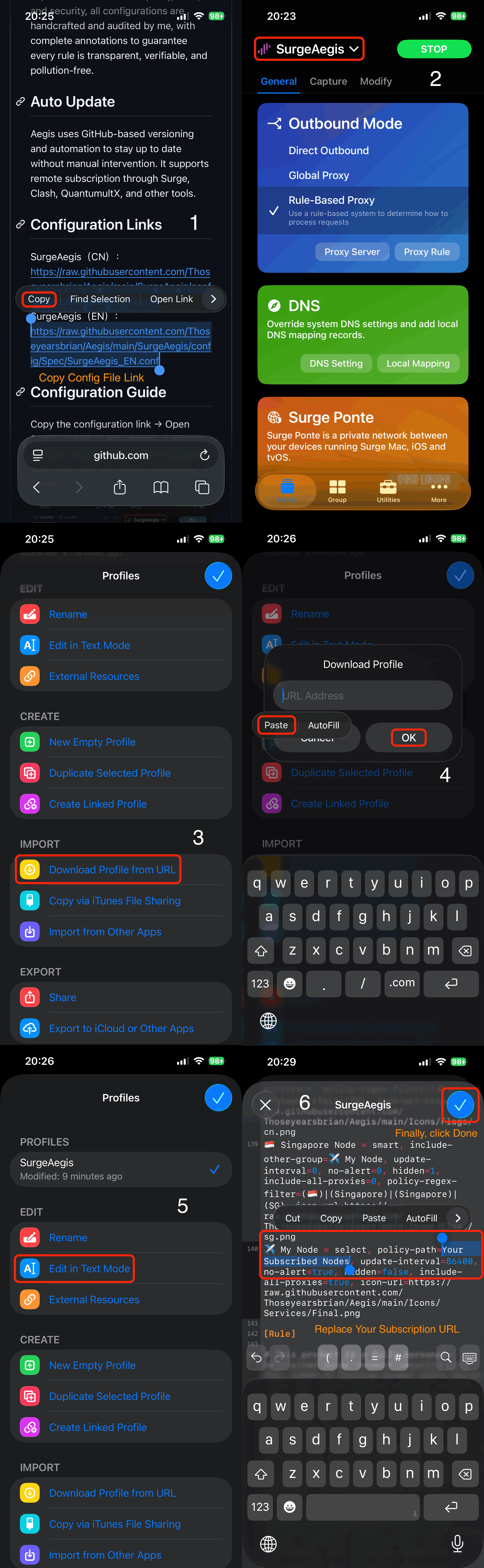
Aegis (CN): https://raw.githubusercontent.com/Thoseyearsbrian/Aegis/main/config/Aegis_CN.conf
Aegis (TC): https://raw.githubusercontent.com/Thoseyearsbrian/Aegis/main/config/Aegis_TC.conf
Aegis (EN): https://raw.githubusercontent.com/Thoseyearsbrian/Aegis/main/config/Aegis_EN.conf
Aegis (CN): https://raw.githubusercontent.com/Thoseyearsbrian/Aegis/main/config/Aegis_IPv6_CN.conf
Aegis (TC): https://raw.githubusercontent.com/Thoseyearsbrian/Aegis/main/config/Aegis_IPv6_TC.conf
Aegis (EN): https://raw.githubusercontent.com/Thoseyearsbrian/Aegis/main/config/Aegis_IPv6_EN.conf
Warning
Please choose the appropriate configuration based on your network environment. If your network natively supports IPv6, use the IPv6 version; otherwise, use the IPv4 version. Do not mix configurations, as this may result in request failures or DNS resolution issues.
Copy the configuration link → Open Surge → Download from URL → Paste the link → Edit in Text Mode → Replace your node with the correct parameter → Done!
Follow the steps below to enable the GeoIP database for the first time:
Open Surge -> More -> General -> GeoIP Database -> Update Now -> Done!
Aegis supports GEOIP lookup rules for countries outside mainland China, as the current database covers global IP ranges.
Aegis enables by default:
GEOIP,CN,DIRECT # GEOIP match for Mainland ChinaTo simplify international traffic routing for general users and reduce access issues, Aegis provides an optional regional routing feature supporting the following regions:
# GEOIP,US,Proxy # Route US region traffic through proxy (enables access to US-based sites)
# GEOIP,GB,Proxy # Route UK region traffic through proxy (enables access to UK-based sites)
# GEOIP,FR,Proxy # Route France region traffic through proxy (enables access to France-based sites)
# GEOIP,DE,Proxy # Route Germany region traffic through proxy (enables access to Germany-based sites)
# GEOIP,RU,Proxy # Route Russia region traffic through proxy (enables access to Russia-based sites)
# GEOIP,EU,Proxy # Route EU region traffic through proxy (enables access to most Europe-based sites)
# GEOIP,AU,Proxy # Route Australia region traffic through proxy (enables access to Australia-based sites)
# GEOIP,JP,Proxy # Route Japan region traffic through proxy (enables access to Japan-based sites)
# GEOIP,KR,Proxy # Route South Korea region traffic through proxy (enables access to Korea-based sites)
# GEOIP,SG,Proxy # Route Singapore region traffic through proxy (common Southeast Asia node)Activation steps:
macOS: Open Surge -> Rules -> Optional Regional Routing -> Check the desired country entries -> Done!
iOS: Open Surge -> Aegis Configuration -> Edit in Text Mode -> Optional Regional Routing -> Remove the “# ” before the corresponding country rule -> Done!
Tip
If the country you want is not listed above, you can manually add the corresponding country code at the end of the configuration, as the current database supports global GEOIP lookups.
Please select the platform you are using and visit the corresponding video tutorial page:
Beginner-Friendly Surge Guide · iOS (4K) | Click the cover image to watch on YouTube
Beginner-Friendly Surge Guide · macOS (4K) | Click the cover image to watch on YouTube
-
Rule Mode is mandatory — otherwise, Aegis’s rule-based identification, routing, and protection capabilities may not function properly
Aegis is a personal digital firewall system built entirely on Surge’s Rule Mode. It relies on rule-based matching to classify domains, enforce policies, and block malicious traffic. Full functionality is only available when Surge is running in **Rule Mode**. If you switch to Global Mode or Direct Mode, network access may still work, but some identification, classification, and policy-based routing capabilities that rely on rule matching may not function properly, resulting in the following risks: - Domains and IPs may not be identified or classified according to rules - Module strategies that rely on rule matching may not function properly - Aegis’s routing, protection, and identification capabilities may not work in full If you encounter a domain temporarily inaccessible due to unmatched rules, you may **switch to Global Mode or Direct Mode temporarily** to regain access. However, we strongly recommend submitting an Issue immediately, so we can update the corresponding rule set and prevent future disruption.
-
It is recommended to combine China.list (for domain matching) and GEOIP,CN (for IP segments) for accurate detection of Chinese traffic:
RULE-SET,https://raw.githubusercontent.com/Thoseyearsbrian/Aegis/main/rules/China.list, DIRECT # Precisely matches Chinese domains GEOIP,CN,DIRECT # Matches traffic from Chinese IPs not in domain list FINAL,REJECT # Final fallback rule (do NOT place GEOIP below this)
-
Supports GEOIP query rules for countries outside mainland China, as the current database supports global country IP ranges.
GEOIP,US,Proxy # Valid GEOIP,AU,Proxy # Valid GEOIP,CN,DIRECT # Valid
-
Explanation for the message “tun-excluded-routes parameter configured, may cause issues after switching networks”
This message is not an error or conflict but a system-level reminder from Surge. It can be safely ignored in a fixed network environment. If you experience temporary LAN communication issues (e.g., AirDrop, Bonjour, or NAS) after switching networks such as Wi-Fi ↔ hotspot, select “Stop Proxy” → “Start Proxy” in the menu to rebuild the routing table and restore connectivity.
This project is built upon inspiration and reference from numerous outstanding open-source initiatives within the GitHub community. We extend our sincere gratitude to all developers who have contributed to the open-source ecosystem.
To meet personal cybersecurity requirements, this project has been deeply customized and optimized for enhanced security based on existing rule sets. In order to ensure the integrity, safety, and long-term availability of the project, all materials and rule files are self-hosted within this repository, thereby avoiding issues such as update failures or trust concerns arising from third-party dependencies.
@Rabbit-Spec 👉 The primary reference for the overall project architecture and rule logic. The current version has undergone extensive restructuring and security adaptation based on this foundation.
@AmnestyTech 👉 Provided Pegasus–related IOC data, serving as a key intelligence source for rule construction (CC BY 2.0 License).
@ESET 👉 Provides data from the public malware-ioc repository, serving as an important source of intelligence for APT-related rule development (BSD 2‑Clause License).
@mieqq 👉 A key contributor to the Chinese Surge community. The mieqq repository has consistently maintained a variety of rules and modules, playing a significant role in the early development and promotion of the ecosystem.
@Sukka 👉 A key developer in rule engineering and distribution infrastructure. The ruleset.skk.moe project provides high-quality rule distribution services for multiple clients and has played an important role in the structural development of the ruleset ecosystem.
The above acknowledgements are listed in no particular order. If you believe your work is missing from the acknowledgements, please feel free to contact me — I will add it promptly.
This project is a non-profit, open-source security rule set aimed at helping users enhance their network defense capabilities. By using this project, you acknowledge that you have read, understood, and agreed to the following terms:
- Third-Party Source Notice: Portions of this project reference publicly available threat intelligence (e.g., security community reports, threat databases, GitHub projects). All such references are properly cited. If you believe there is an issue, please contact us for correction or removal.
- Module Activation Statement: This project adheres to the principles of technical neutrality, information transparency, and independent autonomy. The rule set is designed to assist users in identifying potentially risky communication behaviors. All identification modules are disabled by default. The formulation and activation of related strategies are entirely at the user’s own discretion. The project author assumes no responsibility for any communication risks resulting from user configurations.
- False Positive Warning: As the rule sets may include generalized blocking strategies, users are advised to conduct thorough testing before deployment to ensure normal business operations are not affected. The project author bears no responsibility for connection disruptions, functional issues, or other consequences caused by false positives.
- Commercial Use Notice: This project is released under the Apache License 2.0. You are free to use it for both commercial and non-commercial purposes, provided you comply with the license terms, including attribution and documentation requirements. We strongly oppose abuse of the rule set for closed-source development, infringement of public interest, or any actions contrary to the spirit of open-source.
- No Warranty Clause: This project is provided “as is” without any express or implied warranties regarding its completeness, accuracy, timeliness, or suitability. Users must assess applicability on their own and bear all associated risks.
- Usage Restrictions: All rules and configuration files are intended solely for lawful purposes such as network defense, traffic identification, and security research. Any use for offensive actions, reverse engineering, audit bypassing, or illegal activities is strictly prohibited.
- Limitation of Liability: The project author shall not be held liable for any direct or indirect damages (including but not limited to data breaches, business disruption, or security failures) resulting from the use, replication, or distribution of this project.
- Right to Modify: The project author reserves the right to update, modify, or remove any content or disclaimer clauses at any time without prior notice. It is recommended that users periodically review the repository for the latest version.
Author’s Statement: This project does not engage in malicious activities, does not include hidden backdoors or monitoring mechanisms, does not promote proxy services, and contains no obfuscated or harmful logic. All rule contents are written in plain text, fully commented, structured clearly, and hosted solely within this repository for community review, audit, and traceability.
Copyright and Distribution Notice: This project is licensed under the Apache License 2.0. You may use, modify, and distribute this project — including for commercial purposes — provided that you comply with the terms of the license.
This project upholds the principles of open source and advocates for a healthy, sustainable open-source ecosystem:
- Please retain the original author attribution and license notice.
- Please preserve key annotations and source references to ensure auditability and traceability.
- Do not misuse the rule set in ways that violate the spirit of open source or harm the public interest.
Additionally, the Aegis project has enabled GPG commit signing to ensure the authenticity and integrity of its codebase. You may verify each commit through its GPG signature to gain higher assurance that the code has not been tampered with.
To ensure the security, integrity, and auditability of the rule sets, and to support long-term maintenance and continuous validation, we recommend distributing and using them via remote reference:
Note
- Prefer using
RULE-SETor the official configuration subscription links. - Avoid directly copying and statically maintaining the full rule contents over time.
- If repackaging or integrating the rules, please retain the original reference source to ensure users can access the latest rule data.
Warning
Directly copying and statically maintaining the rule contents may lead to:
- Version drift and rule invalidation;
- Missing critical security updates;
- Overlooking newly added threat intelligence or false-positive fixes;
- Increased maintenance burden and trust risks.